Distributed spam distraction (DSD) is a growing concern in today's digital landscape. With the proliferation of spam emails and messages, individuals and organizations need to be aware of this disruptive cyberattack. In this article, we will explore the concept of DSD, its implications, and ways to mitigate its effects.
Protecting against distributed spam distraction
7 Reasons Microsoft 365 backup is nonnegotiable

Thanks to its comprehensive productivity applications and cloud-based collaboration tools, Microsoft 365 has been instrumental in facilitating remote work for businesses of all sizes. However, amidst the convenience and efficiency offered by this powerful platform, it's crucial for you not to overlook the importance of securing your stored information and enhancing data recovery within Microsoft 365. While Microsoft 365 offers robust built-in security measures and reliable cloud storage, it's important to recognize that data loss or corruption can still occur.
Top VoIP tips to enhance clients’ on-hold experience

One of the most overlooked aspects of customer experience is the on-hold experience. When clients are put on hold during a call, businesses often miss the opportunity to engage and impress them. Fortunately, by making the most of the following Voice over Internet Protocol (VoIP) features, you can turn those moments of waiting into valuable interactions that leave your clients feeling satisfied and valued.
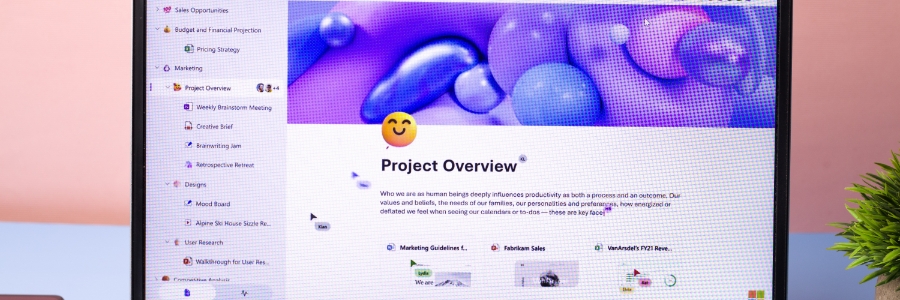
Getting started with Microsoft Loop: A beginner’s guide for Outlook and Teams
Worried about ransomware attacks? Here’s how your company should prepare for them

In recent years, ransomware attacks have become a major threat to businesses of all sizes and industries. These attacks involve the malicious encryption of a company's data, with the attacker demanding payment in exchange for the decryption key. Such attacks can have devastating consequences, including the loss of sensitive information, operational downtime, and reputational damage, to name a few.
Staying afloat: The importance of a business continuity plan for SMBs
5 Crucial steps to increasing BYOD security

Bring your own device (BYOD) arrangements have become increasingly popular in today's workplace, enabling employees to use their personal devices to access work-related applications and data. However, BYOD also presents a security risk, as personal devices may not be as thoroughly protected as corporate devices.
Here’s how to fix the most common VoIP issues
Why data backup is the most important thing you’ll do all year

Whether it’s because of a stolen, damaged, or corrupted device, data loss is an all-too common dilemma that everyone wants to avoid. And while the loss of personal files is disastrous enough, business data that is stolen or tampered with can result in legal disputes, reputational damage, and financial losses in the millions.
When to use Groups, Teams, and Yammer

In the digital age, businesses and organizations have a variety of collaboration tools at their disposal. With so many options available, it can be challenging to determine which tool is best suited for specific tasks and goals. Three commonly used tools in the Microsoft ecosystem are Groups, Teams, and Yammer.