Cybercriminals continue to steal data from unwitting businesses and individuals for their own gain. According to the FBI, the total cost of reported cybercrimes in 2019 was in excess of $43.5 billion. A growing number of cyberattacks also target small- to medium-sized businesses (SMBs), so it’s a good idea to regularly conduct security awareness training sessions for your employees.
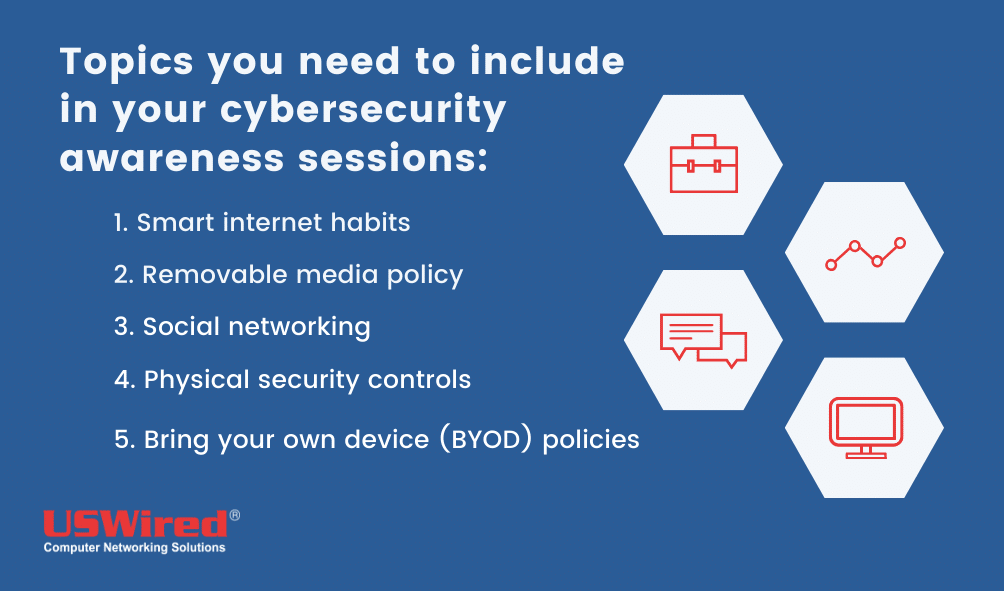
But what topics should you include in your future cybersecurity meetings? Here are some ideas:
#1. Smart internet habits
Your security awareness training program should teach employees about safe internet habits and good cybersecurity hygiene. This means employees must understand how to:
-
Identify and avoid phishing scams. Teach employees to avoid opening suspicious-looking email attachments and links. For starters, tell them to be careful of unsolicited emails with suspicious attachments and links. These may be a part of a phishing scam designed to steal login credentials and other sensitive information.
Also, warn them of installing software programs or downloading files from unsafe websites, as these could be malware in disguise. They could verify a website's safety based on whether the URL link is prefixed with an “https” and a lock icon.
-
Use passphrases instead of passwords. Passphrases such as “antennaedefameoverbillplunging” or “glacierfreightdomainefficient” are much harder to guess for hackers but easier to remember for the user, therefore making them an ideal solution to securing data.
-
Enable multifactor authentication (MFA). On top of passwords, MFA uses multiple user verification methods such as a one-time SMS code, smartphone prompt, or face or fingerprint scan. Even if hackers get ahold of a user’s password, they won’t be able to access the account and steal data unless they have access to the other verification methods.
-
Encrypt laptops. An unencrypted laptop is susceptible to data theft if they go missing or get stolen.
#2. Removable media policy
Removable media like USB drives and external hard drives make file sharing in the office easy. However, you never know where they came from, who used them, and whether they contain viruses or other harmful programs.
Malware embedded in USB drives are designed to spread to other devices on your network as soon as they’re plugged into your company PCs. Some rogue USBs are even capable of granting cybercriminals remote access to company devices, allowing them to steal sensitive information.
That’s why it’s important to teach your employees about USB drop attacks, a social engineering tactic whereby cybercriminals leave USB devices for unwitting people to find and plug into their computers. You should also create policies barring employees from inserting unauthorized flash drives into corporate devices unless they have been deemed safe. For extra protection, you should disable USB drives on their PCs to safeguard company files.
#3. Social networking
Businesses utilize social networking sites to build a brand and generate online sales. But like email, they can also be used to launch phishing attacks. For instance, spam comments on your Facebook page can contain links that lead to phishing sites that try to trick users into handing out information such as usernames and passwords to online accounts.
To prevent data theft, your organization must have an effective social networking program that limits the use of Facebook, Twitter, Instagram, and other services.
#4. Physical security controls
Train employees to be careful of letting unknown individuals inside the office. These include allowing visitors to connect to the office Wi-Fi, leaving handwritten login credentials on one’s desk, or leaving a computer unlocked for the night.
One of the most common physical security issues is tailgating. This occurs when an employee uses their keycard to open a restricted entrance, but is unaware that someone else has snuck in behind them. Another is piggybacking, which involves intruders entering the office by befriending and tagging along with an employee who has authorized access to the building.
#5. Bring your own device (BYOD) policies
Mobile devices like smartphones, laptops, and tablets are increasingly being used by employees to get work done. Besides the convenience and familiarity, they make it easier for users to work from any location.
Find a way to secure your business!
Read our free eBook: 3 Types of Cyber Security Solutions Your Business Must Have and find out how to protect your business and optimize your solutions without breaking the bank
Without regulation and supervision, however, mobile devices can put your data’s safety at risk. For instance, if a user connects to the internet via an unsecured Wi-Fi network, cybercriminals can intercept the connection to steal sensitive company files.
Make sure employees know to avoid public hotspots like the ones in cafes, airports, and local parks. If they do need to access work files on the go, they should use 4G connections and a virtual private network (VPN) to keep their web activity hidden from any hackers monitoring the same networks.
Create rules for using personal mobile devices for work. Set a time and place where employees can access company data using their smartphones or laptops. For example, your staff can only access corporate data while on the office premises, and when they leave for the day, their access should be revoked.
Along with teaching good cybersecurity habits to your employees, partnering with a managed IT services provider like USWired is also important. We provide holistic cybersecurity solutions and proactive system maintenance and monitoring to keep threats at bay, allowing you to focus on growing your business. If your business is in the San Jose or San Francisco Bay Area, we can help you. Download our FREE eBook or call us today to find out what solutions you need to keep your business safe.